Requirements for SAP HANA
To register your SAP HANA source and protect your databases, be sure you meet the requirements.
Prerequisites
Before you register your SAP HANA deployment as a source with Cohesity and protect SAP HANA databases, ensure the following prerequisites:
-
Identify the node(s) in your SAP HANA cluster with adequate resources to execute the SAP HANA connector agent.
-
Synchronize the SAP HANA Linux machine time with a Network Time Protocol (NTP) server. For detailed instructions, see How to Sync Linux Server Time with an NTP Server.
-
Ensure the NTP time is in sync between the client and the SaaS Connector. Perform the following on the client:
-
Verify if NTP is enabled and synchronized in the client using the following command:
timedatectl
-
If the NTP time is not synchronized, use the following command to synchronize the NTP time
timedatectl set-ntp true
-
-
Use "
bash" shell to install the SAP HANA Connector and to run backups and restore workflows of SAP HANA databases. -
A database user with database admin user privileges.
-
Download and install the Cohesity Linux Agent on the SAP HANA node.
-
Download and install the SAP HANA connector agent on the SAP HANA host.
Supported Versions
For more information on supported SAP HANA versions, see Supported Software for Cohesity Cloud Protection Service.
Port Requirements
You must open certain ports in the firewall to allow the Cohesity SaaS Connector(s) to transmit and receive data. The following ports should be opened in the firewall to allow data transfer between the SAP HANA system and the Cohesity SaaS Connector(s):
| Source | Destination | Port | Protocol | Purpose |
|---|---|---|---|---|
| SAP HANA host | SaaS Connector | 11117 (secure gRPC) | gRPC | Required for Backup and Recovery operations. |
Considerations
Review and understand the following before you protect your SAP HANA database:
-
SAP HANA 1.0 is not supported.
-
Indexing is not supported.
-
Helios reporting is not supported with the SAP HANA connector.
-
Scheduling log backups in the Cohesity Cloud Protection Service is not supported, as SAP HANA automatically performs log backups.
-
You cannot cancel a running restore operation.
Create the Secure User Store (hdbuserstore) Key
Create the SAP HANA hdbuserstore key to connect to SYSTEMDB. For detailed instruction, see Secure User Store (hdbuserstore). Use the following command to create the hdbuserstore key:
hdbuserstore SET <KEY> <host:port> <USERNAME> <PASSWORD>
Ensure that the user account of the secure user store has the following administrator privileges:
-
BACKUP ADMIN
-
DATABASE ADMIN
-
DATABASE START
-
CATALOG READ
-
MONITORING
Sample:
hdbuserstore SET SYS_KEY test-FI:30013 SYSTEM testpassword
After you have created the hdbuserstore key, verify if the key has the required SAP HANA connection information, such as hostname or login credentials. Verify the key using the following command:
tecadm@test-FI:/usr/sap/TEC/home> hdbsql -AU SYS_KEY "select DATABASE_NAME,ACTIVE_STATUS from m_databases" | DATABASE | ACT | | -------- | --- | | SYSTEMDB | YES | | TEC | YES | | SRC | YES | | DST | YES | 4 rows selected (overall time 28.150 msec; server time 659 usec) tecadm@test-FI:/usr/sap/TEC/home>
Download and Install the Cohesity Linux Agent
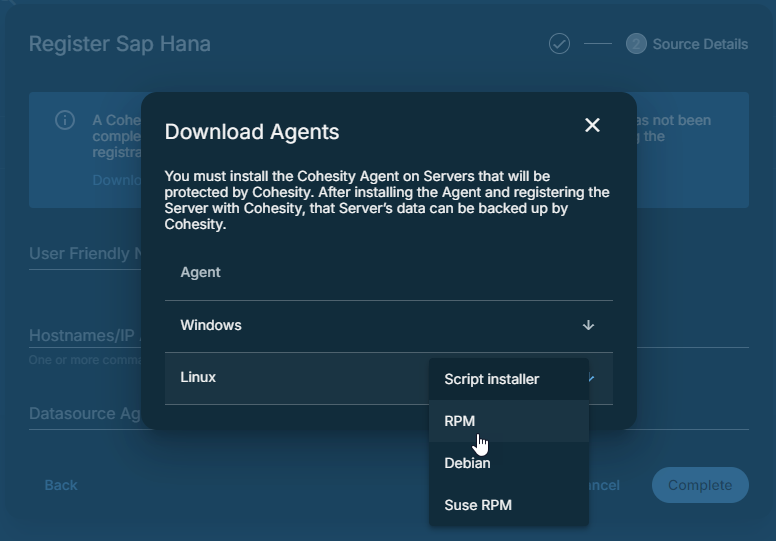
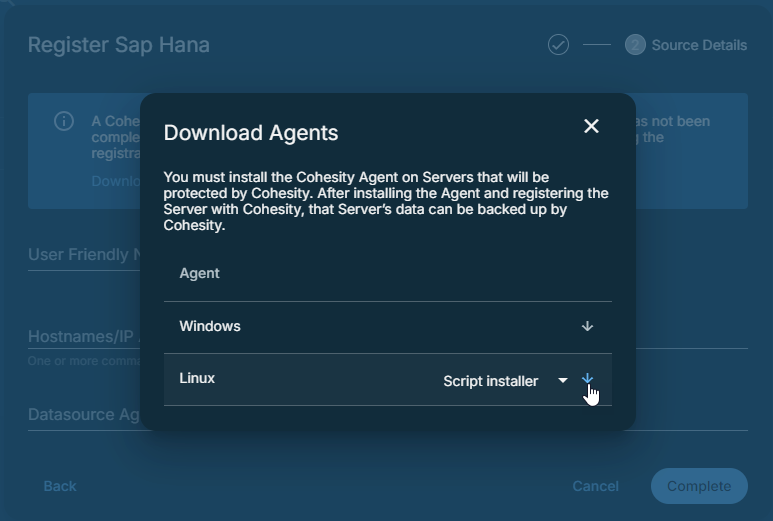
The Cohesity Linux Agent is available as a script-based, RPM, Debian, and SUSE RPM Installer Package. Based on your requirements, download the installer and install it on the SAP HANA node(s).
Download the Cohesity Linux Agent
To download the Cohesity Linux Agent:
-
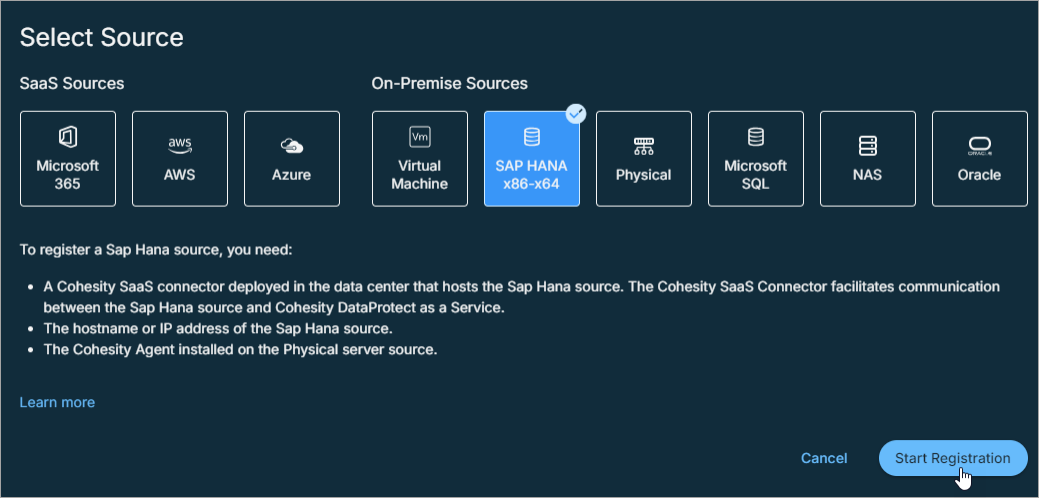
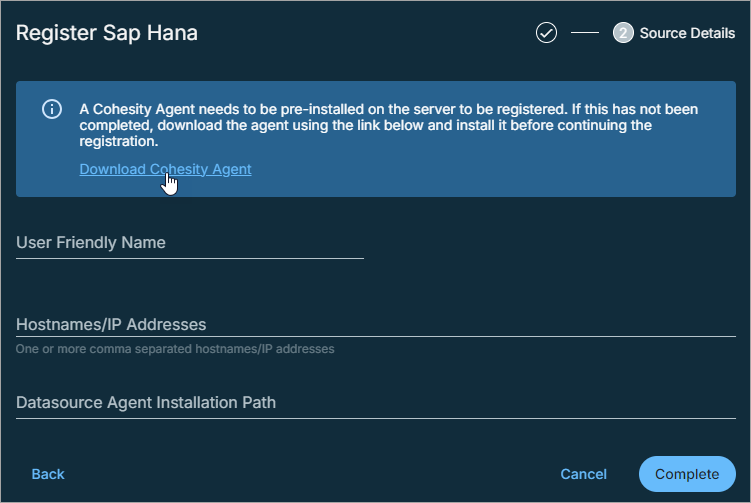
In Cloud Protection Service, navigate to the Sources page and click + Register Source in the upper-right corner of the page.
-
In the Select Source dialog box, select SAP HANA and then click Start Registration.
-
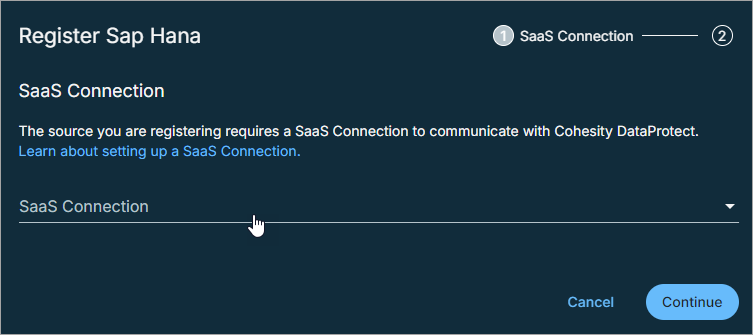
In the Register SAP HANA dialog box, select an existing healthy SaaS connection marked Unused, or click Create SaaS Connection, follow the instructions in Create a SaaS Connection, and then click Continue.
-
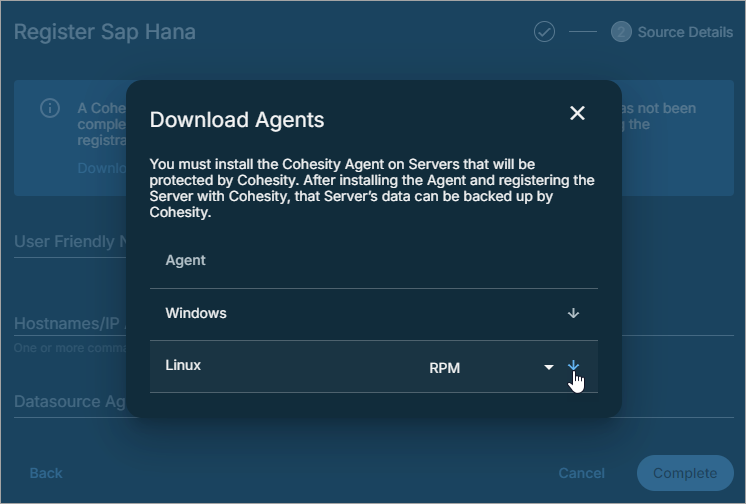
Click Download Cohesity Agent.
-
In the Download Agents dialog box, under Linux, select the Cohesity Agent installer package from the drop-down menu and then click the download icon.
Install RPM, Debian or SUSE RPM Installer Package
The following table explains the action to be performed for installing the RPM, Debian or SUSE installer package:
In the following commands, replace the Cohesity agent version with the desired agent version.
| Action | How to |
|---|---|
| Download the Agent installer |
From the Download Agents window, based on your Linux distribution, select RPM, Debian, or SUSE RPM and download it to the server you want to protect. For detailed instructions, see Download the Cohesity Linux Agent.
|
| Navigate to the downloaded directory | As the root user with local system privileges on that server, change the directory to the location of the installer package. |
| Install the Custom certificates |
LINUX If you are using a Cohesity certificate then run the following commands to install the user certificate followed by agent installation: export ENFORCE_USE_CUSTOM_CERTS=true && export AGENT_CERT_FILE=<path-to-agent-certificate-in-Cohesity-format> If you are using a user certificate then run the following commands to install the user certificate followed by agent installation: export ENFORCE_USE_CUSTOM_CERTS=true && export USE_THIRD_PARTY_CERTS=true && export ROOT_CA_FILE=<path-to-root-ca-cert> && export PRIVATE_KEY_FILE=<path-to-server-private-key> && export CERT_CHAIN_FILE=<path-to-server-cert> |
| Install the Agent |
Run the following command depending on the installer package:
|
| Install the agent as root user |
Run the executable file with the following command syntax: /<path_to_installer_file> -- --install -c 0 -S root -G root Followings are the command options in details:
|
| Install the agent as non-root user |
To start the service as a non-root user, create a new user or use an existing user with sudo permission and run the following command:
|
| Location |
|
Install Script Installer Package
The following table explains the action to be performed for installing the script installer package:
In the following commands, replace the Cohesity agent version with the desired agent version.
| Action | How to |
|---|---|
| Download the Agent installer |
From the Download Agents window, based on your Linux distribution, select Script Installer and download it to the server you want to protect.
|
| Navigate to the downloaded directory |
As the root user with local system privileges on that server, change the directory to the location of the installer package. For SLES 11 SP4, installing the agent as the root user is required. |
| Make the installer executable |
Make the installer executable, for example: |
| Install the Agent |
Run the executable: sudo /cohesity_agent_<version>_linux_x64_installer – --install |
| Location |
|
Download the SAP HANA Connector Agent Installer
Cohesity provides a SAP HANA Connector for backing up and restoring SAP HANA databases. The connector is available as either an RPM-based or script-based installer.
Download the RPM-Based Installer
To download the RPM-based SAP HANA Connector Agent:
-
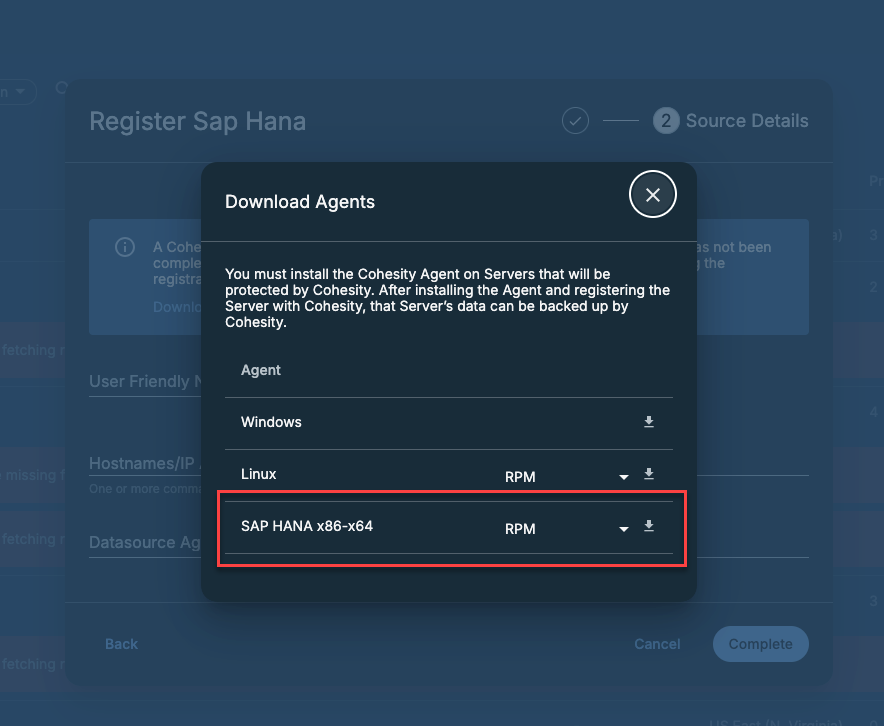
Follow Steps 1 to 5 in the Download the Cohesity Agent for Linux section.
-
In the Download Agents window, locate SAP HANA x86-x64, select RPM, and download the installer.
Download the Script-Based Installer
The script-based SAP HANA Connector installer is available on the Cohesity Download portal. Log in to the portal and download the installer to the SAP HANA host.
Install the SAP HANA Connector Using RPM Based Installer
Before you install the SAP HANA Connector Using RPM-based installer, ensure that you configure the following environment variables on the SAP HANA machine:
| Environment Variable | Description | Mandatory? | Command |
|---|---|---|---|
SID
|
The <SID>adm user account that must own the backup files on the Cohesity view. If you have not created the user account, then create an Operating System (OS) user account in the following format: <SID>adm. Where <SID> is a unique three-character code called SAP System Identification (SID). It is available for every R/3 installation (SAP system) that consists of a database server and several application servers.
|
Yes | export SID=<VALUE> |
SYSTEMDB_KEY
|
The SAP HANA HDBUSERSTORE key to connect to the SYSTEM DB. | No | export SYSTEMDB_KEY=<HDBUSERSTORE key> |
| DEBUG | Option to enable installer debug. Supported values are 1 or 0. | No | export DEBUG =<VALUE>
|
To install the SAP HANA connector using rpm-based installer:
- Log on to the SAP HANA node’s bash CLI using root or user with sudo access.
-
Make the SAP HANA connector installer
(cohesity-hana-backint-<version>.x86_64.rpm) executable using the following command:> chmod +x cohesity-hana-backint-<version>.x86_64.rpm
-
Install the SAP HANA connector using the following command:
> sudo -E rpm -ivh cohesity-hana-backint-<version>.x86_64.rpm
Install the SAP HANA Connector Using Script Based Installer
To install the SAP HANA connector using script-based installer:
-
Log on to the SAP HANA node’s bash CLI using
<SID>admuser. -
Make the SAP HANA connector installer (
cohesity_secure_connector_service_7.2.1c_sap_hana_installer) executable using the following command:SAP_HANA_SERVER:/home/adminse # chmod +x cohesity_secure_connector_service_<version>_sap_hana_installer
During the SAP HANA connector installation, by default, the script installer extracts the files to the
/tmpdirectory. If you plan to extract the files to a different directory, you can define the directory path in theTMPDIRenvironment variable as follows:export TMPDIR=<directory_path>. -
Install the SAP HANA connector using the following command:
./cohesity_secure_connector_service_<version>_sap_hana_installer -- --install --install-dir=<backint install directory> --sid=<SID> --systemdb-key=<systemdb_key> --workflow=<workflow>
You can view the details of SAP HANA Connector installer options using the
--helpoption. For example:./cohesity_secure_connector_service_sap_hana_installer --helpWhere:
Options Mandatory? Description --install-dirNo The directory on the SAP HANA node on which you want to install the SAP HANA connector.
If
--install-diris not specified, the SAP HANA connector is installed in the/usr/sap/${SAPSYSTEMNAME}/homedirectory.--sidNo SAP System Identification (SID) is a unique three-character code that is available for every R/3 installation (SAP system), which consists of a database server and several application servers. --systemdb-keyYes The SAP HANA HDBUSERSTORE key to connect to the SYSTEM DB. If you plan to backup your SAP HANA databases using the SAP HANA connector, ensure that you use the option
--systemdb-key <user_store_key>.--debugNo Option to enable installer debug. After the SAP HANA connector is installed, the SAP HANA connector agent are available at:
<backint_install_directory>/cohesity_backint_plugin/uda_scriptsFor example:
/usr/sap/SID/home/cohesity/cohesity_backint_plugin/uda_scripts
-
Log on to the SAP HANA node as root user and create a soft link of
<backint_install_directory>/cohesity_backint_plugin/uda_scriptsfolder to/opt/cohesity/agent/uda_scriptsusing the following command:ln -s /usr/sap/SID/home/cohesity/cohesity_backint_plugin/uda_scripts /opt/cohesity/agent/uda_scripts
Before creating the soft link, make sure to remove any existing soft link to the
<backint_install_directory>/cohesity_backint_plugin/uda_scriptsfolder.
Uninstall the SAP HANA Connector
To uninstall the SAP HANA connector, run the following command with appropriate parameters on SAP HANA node’s bash CLI.
Using the RPM installer:
> sudo -E rpm -evh cohesity-hana-backint-<version>.x86_64.rpm
Using the Script installer:
./cohesity_secure_connector_service_<version>_sap_hana_installer -- --uninstall --install-dir=<backint_install_directory> --sid=<sid> --workflow=<workflow>
Specify the --standby option, if you are uninstalling the SAP HANA connector on a standby node.
After you have successfully uninstalled the SAP HANA connector, log on to the SAP HANA node as root user and unlink the soft link from /opt/cohesity/agent/uda_scripts.
Upgrade the SAP HANA Connector
To upgrade the SAP HANA connector, run the following command on all SAP HANA nodes.
Using the RPM installer:
> sudo -E rpm -Uvh cohesity-hana-backint-<version>.x86_64.rpm
Using the Script installer:
./cohesity_secure_connector_service_<version>_sap_hana_installer -- --upgrade --install-dir=<backint_install_directory> --sid=<sid> --systemdb-key=<user_store_key> --workflow=<workflow>
After you have upgraded the SAP HANA connector, log on to the SAP HANA node as root user and create a soft link of <backint_install_directory>/cohesity_backint_plugin/uda_scripts folder to /opt/cohesity/agent/uda_scripts using the following command:
ln -s /usr/sap/SID/home/cohesity/cohesity_backint_plugin/uda_scripts /opt/cohesity/agent/uda_scripts